Health Insurance Portability and Accountability Act (HIPAA)
Healthcare Data Privacy in Geocoding Services
HIPAA is a USA law governing health insurance portability and the accountability of organizations handling protected health information. Similar to GDPR (see how we address GDPR), it focuses on regulating privacy of individuals when healthcare information is obtained. The approach is to create giant and complex set of workflows that deals with personal identifiable information and the preventions and distribution of it.
Protected health information (PHI) tries to identify and protect the distribution of such privacy information when permitted by law or internal regulations.
There are at least 18 type of identifiers that fall under the PHI.
- full or partial patient names;
- All geographical subdivisions smaller than a State, including street address, city, county, precinct, zip code, and their equivalent geocodes, except for the initial three digits of a zip code, if according to the current publicly available data from the Bureau of the Census: (1) The geographic unit formed by combining all zip codes with the same three initial digits contains more than 20,000 people; and (2) The initial three digits of a zip code for all such geographic units containing 20,000 or fewer people is changed to 000.
- All elements of dates (except year) for dates directly related to an individual, including birth date, admission date, discharge date, date of death; and all ages over 89 and all elements of dates (including year) indicative of such age, except that such ages and elements may be aggregated into a single category of age 90 or older;
- Phone numbers;
- Fax numbers;
- Electronic mail addresses;
- Social Security numbers;
- Medical record numbers;
- Health plan beneficiary numbers;
- Account numbers;
- Certificate/license numbers;
- Vehicle identifiers and serial numbers, including license plate numbers;
- Device identifiers and serial numbers;
- Web Universal Resource Locators (URLs);
- Internet Protocol (IP) address numbers;
- Biometric identifiers, including finger and voice prints;
- Full face photographic images and any comparable images; and
- Any other unique identifying number, characteristic, or code (note this does not mean the unique code assigned by the investigator to code the data)
There are two approaches when dealing with PHI and HIPAA.
One is to create very isolated and sterile data centers where the information is considered "safe".
Then when transmitting across internet to third party providers, like online geocoding tools, the third parties must have similar sterile data environment.
This approach is very expensive and does not guarantee any safe distribution of data as third parties providers may be in compliant one day and next day they may be bought by another third party, go out of business , or simply drop the guard for some reason. In addition, there is no guarantee that hacking may not occur in any of these data centers.
A better and more sound approach is to separate medical information and PHI at the medical data centers.
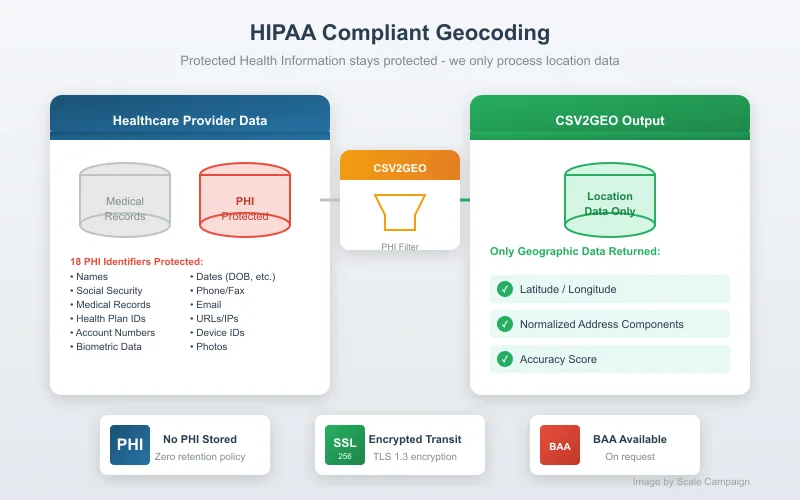
on the left, the data centers have separated in a very high level their medical information with the PHI information with some links internally indexing the records.
Whoever, when sending out information for geolocation, or reverse geolocation, simply do not send any of the 18 identifiers, except the location. Not even temporary id. Since the data is in order, the sent data will come back in the same order and can be attached safe to the existing PHI information in the data center. In addition, the user who performed the geocoding task can go and delete the task and if necessary the whole account.
The method above is guarantees that no indexes can be linked in the future between csv2geo and the data vendor provider. The approach also established a safe practice at the data vendor data warehouse in general.
Scale Campaign has extensive regulatory experience in the area if additional
help is needed. Please contact us for additional assistance if needed at
![]()